AOG Information Management System (AIMS)
AIMS is a multi-module, multi- site, highly configurable management solution that allows the end user to see consolidated data from federated systems in one easy to access place. Regardless of whether the information is from an internal CIMS module, or an external data source, it is presented as a single source solution for our customers using the customer defined criteria.
What you’ll get
-
✺
Dashboards
(Customizable, role based, and interactive) -
✺
Inventory Management, Contract Financial Management, Mission Tracking, Flight Hour tracking and reporting, property transfers, manning reports, procurement work flow, and many other modules
-
✺
Real-time Information - by providing real-time visibility of work in process to the shop floor, supported by a real-time problem resolution system that extends into supplier networks.
-
✺
Streamlining & Simplifying - Streamlining and simplifying complex work instructions and inspection requirements that are specified as part of work instructions, and include data collection and certification requirements
-
✺
Systematic Process Management - provides delivery of inspection measurements and observations, giving inspectors the option of launching and completing required routine and non-routine instructions.
-
✺
CIMS is a transactional based data system. This means that any action taken within the CIMS is logged and traceable. By maintaining the CIMS as a transactional based system, all historical information is readily available, usable and able to be displayed in a near real-time.
What’s inside
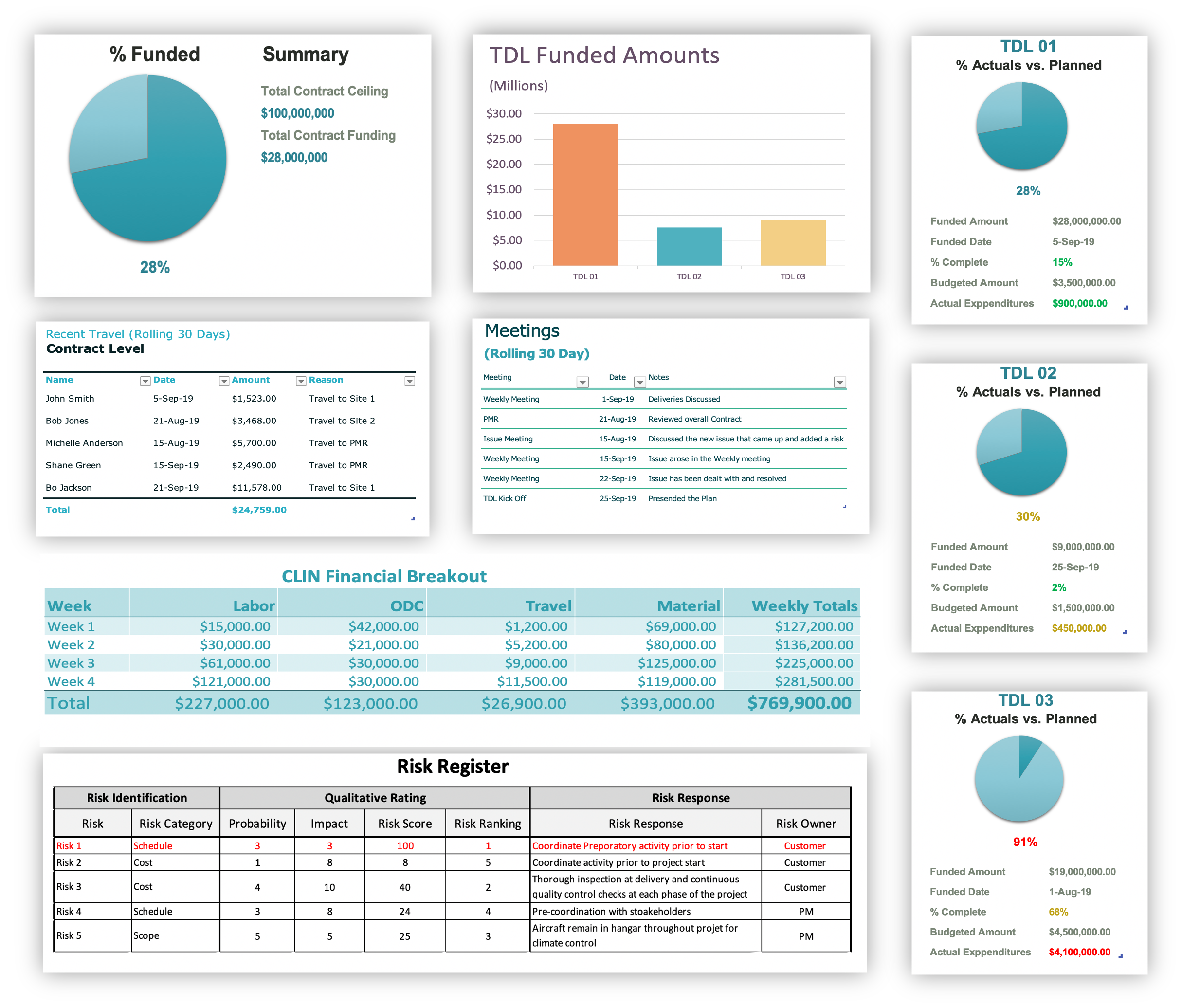
Dashboards
Customizable dashboards lets the users define what they see and how they see it to make sure they are maintaining focus on the most critical items.
Inventory Management
The Inventory Module allows the user to perform all of the required asset transactions in one location within the system instead of the typical cumbersome multi-screened nightmare.
Contract Financial Management
Allowing users the power of seeing all the information surrounds the finances of a project in one, easy-to-use location
AIMS Security
Interface and Database Management
• Encryption in transit - All data is encrypted as it moves between our servers and your web browser. The API is fully encrypted so every request to view or update records automatically encrypts that databehind the scenes.• Encryption at rest - We encrypt all data that's stored on our servers. This includes both the records storedin our databases and search indexes as well as any files and images you've uploaded to yourdatabase.• Bank-level Encryption - We use both SHA-256 and AES-256 encryption, the strongest encryptionavailable. This is the same level of encryption that banks use.• Compliance - AWS environments are continuously audited, with certifications from accreditation bodies across geographies and verticals. Amazon has achieved compliance with the strictestcompliance programs.• DDoS Mitigation - AWS provides a robust platform that is not only pre-built to mitigate some attacks, but italso allows us to react quickly to spread out impact if there is an attack. We've also added safeguardsto underlying servers as an additional level of protection.• Built in Redundancy - AWS uses features like Auto-Scaling and Elastic Load Balancing to ensure that ourproduction systems remain online and traffic is always routed to healthy instances.• SOC 3 and ISO 27001 Certified – It is automatically certified for many stringent security standards byusing AWS as its infrastructure.• Firewalls - We use firewalls to protect every virtual server, database, and load balancer to ensure thatonly authorized traffic is accessing those resources.• Password Protection - Password protect your apps with encrypted password technology, so that onlyauthenticated users can access it. You can configure multiple registration options for adding newusers.• Roles & Permissions - Assign roles for your users and define exactly which permissions each role has.Each page in your interface can be authorized for specific roles.• Record Level Security – We design your application so that each logged-in user can only access therecords that are connected to them.• Password Encryption - All user passwords are double encrypted and hashed with a salt, which preventsdictionary attacks and adds an extra layer of security.• Advanced Logins - Integrate your Active Directory or LDAP users for Single Sign On to limit access to yourestablished users.• Version Tracking - We store every change to every record.• Secure Files - Option to store files behind your logins so only authenticated users can view and download those files.• IP Blocking - Optionally restrict access to your app to specific IP addresses or IP blocks.• Data Encryption - All data displayed in your app and updated back to the database is encrypted andsecured with SSL.